Linux
Keith Smith - My Blog > LinuxInstalling Python 2 on Mac OS XThursday, October 11, 2018 - Posted by Keith A. Smith, in Automation, Linux
OS X comes with a
large number of UNIX utilities, those familiar with Linux systems will
notice one key component missing: a decent package manager. Homebrew fills this void.
Homebrew is a package manager for OS X. A package is a collection of code files that work together. Installing them usually means running a script (a bit of code) that puts certain files in the various directories. A lot of the packages you will want are going to have dependencies. That means they require you to have other packages already installed on your computer. Homebrew will find and install dependencies for you AND it will keep them organized in one location AND it can tell you when updates are available for them. On top of all of that it gives super helpful instructions when everything doesn't go smoothly. You can read more about it at Homebrew's website. For now, install Homebrew using the following line of code: $ /usr/bin/ruby -e "$(curl -fsSL https://raw.githubusercontent.com/Homebrew/install/master/install)" The
script will explain what changes it will make and prompt you before the
installation begins. Once you’ve installed Homebrew, insert the
Homebrew directory at the top of your export PATH="/usr/local/bin:/usr/local/sbin:$PATH" Now, we can install Python 2.7: $ brew install python@2 Because export PATH="/usr/local/opt/python@2/libexec/bin:$PATH" Homebrew names the executable $ python -V # Homebrew installed Python 3 interpreter (if installed)
-End |
 0 Comments 0 CommentsTweet |
Observium - Rename existing devicesTuesday, July 17, 2018 - Posted by Keith A. Smith, in LinuxObservium is one of my go-to open source solutions for network monitoring, I figured I'd share a recent challenge I encountered. I found myself needing to change a few device hostnames in observium, and it can be a bit tricky since it can't be done via the UI. This task can be done successfully from the command-line by running the following: Shell cd /opt/observium/ and execute php rename_device.php old_device_name new_device_name Once you're done renaming your device you should force snmp discovery and the poller to run: Shell execute the following: php discovery.php -h all php poller.php -h all Once the above process is completed you should see your devices renamed in the UI.
-End |
 0 Comments 0 CommentsTweet |
KanboardFriday, January 19, 2018 - Posted by Keith A. Smith, in Linux
What is kanboard?
Kanboard
is an opensource web hosted project management software. So far I think
it’s pretty damn cool. It has all the features of the top paid project
management solutions out there with the little added bonus of it being
free.
The “cost” for anyone working with FOSS will be the setup time. This was my first time trying to setup Kanboard so I figured I would post how it went, I did encounter some stumbling blocks so I noted the solutions I used to get the installation up and running. Hopefully this will reduce the “cost” for you. I tested this on Ubuntu Xenial 16.04 LTS
Installation

I had to do the following to setup email https://github.com/kanboard/kanboard/blob/master/doc/en_US/email-configuration.markdown
I commented out the two bottom lines to make it work.
// Credentials for authentication on the SMTP server (not mandatory) define('MAIL_SMTP_USERNAME', 'username'); define('MAIL_SMTP_PASSWORD', 'super password'); Errors I encountered Internal Error: PHP extension required: “pdo_sqlite” Solution: Run the following in the terminal window sudo apt-get install php7.0-sqlite Internal Error: This PHP extension is required: "dom". sudo apt-get install php-xml
-End |
 0 Comments 0 CommentsTweet |
Applying a “Defense-in-Depth” StrategyMonday, May 22, 2017 - Posted by Keith A. Smith, in Network, VMware, Microsoft, Linux, SecurityIT Teams and Staff can effectively maintain physical and information security with a “defense-in-depth” approach that addresses both internal and external threats. Defense-in-depth is based on the idea that any one point of protection may, and probably will, be defeated. This approach uses three different types of layers (physical, electronic, and procedural) and applies appropriate controls to address different risks that might arise in each. The same concept works for both physical and network security. Multiple layers of network security can protect networked assets, data and end points, just as multiple layers of physical security can protect high-value physical assets. With a defense-in-depth approach: • System security is purposely designed into the infrastructure from the beginning. Attackers are faced with multiple hurdles to overcome if they want to successfully break through or bypass the entire system. • A weakness or flaw in one layer can be protected by strength, capabilities or new variable introduced through other security layers. Typical defense-in-depth approaches involve six areas: physical, network, computer, application, device and staff education. 1. Physical Security – It seems obvious that physical security would be an important layer in a defense-in-depth strategy, but don’t take it for granted. Guards, gates, locks, port block-outs, and key cards all help keep people away from systems that shouldn’t touch or alter. In addition, the lines between the physical security systems and information systems are blurring as physical access can be tied to information access. 2. Network Security – An essential part of information fabric is network security and should be equipped with firewalls, intrusion detection and prevention systems (IDS/IPS), and general networking equipment such as switches and routers configured with their security features enabled. Zones establish domains of trust for security access and smaller virtual local area networks (VLANs) to shape and manage network traffic. A demilitarized zone between public resources and the internal or trusted resources allows data and services to be shared securely. 3. Computer Hardening – Well known (and published) software vulnerabilities are the number one way that intruders gain access to automation systems. Examples of Computer Hardening include the use of: • Antivirus software • Application whitelisting • Host intrusion-detection systems (HIDS) and other endpoint security solutions • Removal of unused applications, protocols and services • Closing unnecessary ports Software patching practices can work in concert with these hardening techniques to help further address computer risks that are susceptible to malware cyber risks including viruses and Trojans etc. Follow these guidelines to help reduce risk: • Disable software automatic updating services on PCs • Inventory target computers for applications, and software versions and revisions • Subscribe to and monitor vendor patch qualification services for patch compatibility • Obtain product patches and software upgrades directly from the vendor • Pre-test all patches on non-operational, non-mission critical systems • Schedule the application of patches and upgrades and plan for contingencies 4. Application Security – This refers infusing system applications with good security practices, such as a Role Based Access Control System,Multi-factor authentication (MFA) also known as (also known as 2FA) where ever possible which locks down access to critical process functions, force username/password logins, combinations, Multi-factor authentication (MFA) also known as (also known as 2FA) where ever possible and etc. 5. Device Hardening – Changing the default configuration of an embedded device out-of-the-box can make it more secure. The default security settings of PLCs, PACs, routers, switches, firewalls and other embedded devices will differ based on class and type, which subsequently changes the amount of work required to harden a particular device. But remember, a chain is only as strong as its weakest link. 6. Staff Education - Last but not least it’s important to talk to staff about keeping clean machine, the organization should have clear rules for what employees can install and keep on their work computers. Make sure they understand and abide by these rules. Following good password practices is important a strong password is a phrase that is at least 12 characters long. Employees should be encouraged to keep an eye out and say something if they notice strange happenings on their computer. Educating Employees at least once a year is important Training employees is a critical element of security. They need to understand the value of protecting customer and colleague information and their role in keeping it safe. They also need a basic grounding in other risks and how to make good judgments online. Most importantly, they need to know the policies and practices you expect them to follow in the workplace regarding Internet safety.
-End |
 1 Comments 1 CommentsTweet |
system_thread_exception_not_handled xen.sys BSODFriday, September 4, 2015 - Posted by Keith A. Smith, in VMware, Xen, Microsoft, LinuxThe system_thread_exception_not_handled xen.sys BSOD issue was interesting to me; 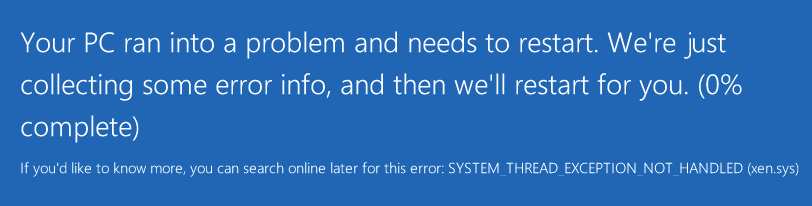 I wanted to see if I could reproduce this. I exported a VM from Amazon's EC2 because Amazon EC2 uses the Xen hypervisor as well. I upload the VM into a datastore on vSphere and convert the virutal disk as I noted here http://bit.ly/1UrCpqN I power on the VM and I get the same system_thread_exception_not_handled xen.sys BSOD. I boot into safe mode I run a msconfig from the search, Under the boot tab I chose base video because I still had the xentools installed on the VM's. So that had to be the culprit right? I reboot the VM, and it boots fine, at this point I uninstall all the XenServer/Citrix related items. I then restart the VM and I was glad to see it make it to the login screen. Solution: I think...  The way to avoid this issue if you are going from Xen to VMware or any other hypervisor is to uninstall all the XenServer/Citrix items before performing the export of the VM.
|
 1 Comments 1 CommentsTweet |



